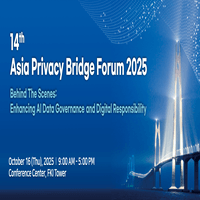
2nd APB Forum, Fall 2016
Humanity in the Digital Intelligence Era
Track A. Asia Privacy Bridge Forum

Data Protection Laws & Regulations in Korea
Hyunjun Kwon (KISA)
In the Korean constitution, the right to privacy and control one’s
personal information are stated as a fundamental right. Korean laws
regarding personal information protection constitute of general and
special laws. The general law is the Personal Information Protection Act (PIPA), whereas the special laws are the Credit Information Law and Information Communications Network Act.
Different rules as regards protection of personal information in Korea
include the Privacy Impact Assessment (PIA) and Personal Information Management System (PIMS).
System and Practice: The Exploration of Private Data Protection in China
Tial Li (Peking University)
China still lacks general laws and has no clear and appropriate ones
regarding personal information protection. Therefore, no laws are
specifically concerned with collecting, saving, sending, and handling
of personal information protection. Although comprehensive personal
information protection laws are lacking, personal information is protected under basic crime and civil law provisions through other laws in several relevant areas. Private data protection in China is under progress. Chinese national leaders are introducing “cybersecurity for citizens and society.”
Act on the Protection of Personal Information and Information Moral
Eiji Aoki (Institute for Hyper Network Society)
In the future, there will be changes in every field, such as ICT and
cars, agriculture, medicine, social infrastructure, retail and marketing, finance, manufacturing, education, media, and business administration. In particular, the importance of personal information continues to grow with the expansion of the Internet of Things (IoT) and Internet of Everything (IoE). In this new environment, new rights should be recognized. For a safer society, there must be an understanding of information morals through ways such as research on righteous ICT.
Cross-Border Data Transfer in Korean Privacy Law Perspective
Taewook Kang (BAE, KIM & LEE LLC)
There are many challenges in applying personal information protection to actual situations. Under the current law, prior to receiving consent to provide personal data, the recipient’s name must be assigned and shared. However, in many situations, distinguishing the recipient when receiving prior consent is difficult.
As the cloud server has become widely used, legal requirements for
permission and notice have created challenges for IT network service providers. Under the cloud server, identifying the location (country) and providing prior legal notice are difficult. For cloud server service provider companies, options other than through receiving comprehensive consent are unavailable.
Moreover, under the assumption that big data are considered “personal data,” as a rule, each user’s consent is necessary when collecting mass data and those from other countries for marketing analysis. However, Korean laws and regulations are ambiguous, and standards for big data are also unclear.
Privacy in the Asia on the Move
Hiroshi Miyashita (Zhou University)
Since the introduction of Big Data and IoT, people do not know to which they are connected. Additionally, as there has been active trans-border exchange of data internationally, individuals and businesses transcend national borders. Cooperation between nations to manage the upcoming privacy issues is vital. The APB Forum should prevent and address possible issues through shared research between nations, exchange of outstanding cases, privacy design contests, various education measures, and promotional and research activities.

Introduction and Improvement of Regulation Regarding Personal Information Cross-border Transfer in China
Wu, Rihuan (China University of Political Science and Law)
Many Korean businesses and transnational corporations are currently working in China and save data abroad, creating the need for personal information cross-border transfer laws. Ass general laws for personal information protection are lacking, many issues have surfaced. Although around 20 laws involve regulations relevant to personal information, the breach of a law on personal information is difficult to punish because of a lack of specificity. In the future, there should be specific regulations for businesses in China to utilize and protect personal information.
Track B. Beyond Digital Gap

Creating a Classification System for Senior Citizens and Investigating Key Requirements for ICT Service Development
Kyungmi Jeong (Yonsei University)
Korea will become an aging society in 2018 and an elderly one in
2026. Current welfare services for the elderly include assisted baths and home care. Other than these services, in reality, the elderly seek jobs and classes appropriate for their demographic groups. There are many healthy and financially secured senior citizens, but the services provided for them do not address adequately the situations mentioned above. Although the elderly and their skills continue to grow, existing services only cater to a minority of elders. Programs that provide assistance to senior citizens in their daily lives should consider factors such as economic status, cognitive skills, emotional state, health condition, and housing situation.
A New Form of Digital Divide in the Digital Age: Focusing on Generational Differences and the Second Divide for the Senior Generation
Yongsuk Hwang (Konkuk University)
Among the main sources of conflict in society is generation gap.
Regarding the media, different generations receive information
through varying sources. In Korean society, surveys on political views and knowledge of the world show highlight such gap. The younger generation uses platforms, such as social media, to receive information and, consequently, obtain messages from groups with similar types of views. In contrast, the information that the older generation receives from the mainstream and traditional media is different. Communication technology is growing rapidly.
Adoption and utilization of technology are a matter of whether citizens obtain life opportunities regarding technology. Policies on digital and cultural resources being equal is a common misconception, as equality of opportunity is at the heart of the issue. Equality of opportunity through digital technology is secured through allowing digital skills to be accessed easily and understood by everyone. The utility of opportunities is maximized as more opportunities are provided.
Why is the Digital Divide a Relevant Topic for Discussion in the Intelligence and Information Age?
Bongsup Kim (National Information Society Agency)
Which factors should be considered to overcome the digital divide in the “smart” era? Broad & Fisher (2004) shared 5C (Connectivity, Capability, Content, Confidence, Continuity) as five viewpoints in the model for overcoming the digital divide.
1) Connectivity: issues of availability and reliability regarding data
communication technology and access to services, and the duty of
policies to secure physical access to infrastructure
2) Capability: digital competency at an institutional and an individual
level, not only using data communication technology but also creating measures for cultivating individual and institutional values
3) Content: offering information services according to the user’s lifestyle through ways relevant to objectives and languages, the importance of accurate recognition, and analysis of the user’s desires
4) Confidence: related to self-efficacy, changing the situation from the
problem of whether one possesses or lacks information to a matter of
the presence or absence of desire for information, measures to continue to increase awareness, and self-efficacy regarding the utility of data communication technology services
5) Community: continuous efforts to connect the real and virtual worlds organically as ICT is integrated into everyday life
FinTech’s Trends in User Certified Technology
Seunghun Jin (ETRI)
FinTech’s main trends can be explained as VIP3 (Variety, Intelligence, Privacy, P2P, Phishing). First FinTech’s certification method offers convenience through diversification, intellectualization, analysis of user activities, and live situation detection. Security is strengthened through continuous confirmations and detection of abnormalities. However, privacy and phishing issues are arising as various information is utilized to provide users with convenience.

Increased Income Inequality Issues from Job Polarization in the Fourth Industrial Revolution
Jisun Lim (Barun ICT Research Center, Yonsei Univ.)
The changes in technology, which arise from the Fourth Industrial
Revolution, allow working conditions for laborers to be flexible and
consumers to become agents in production as a part of the transition
into a prosumer economy through consumer-based production methods. Consequently, issues related to income inequality rather than job creation may arise. Hence, to overcome income inequality issues, the government should reduce hours of labor, offer reeducation for jobs, and enhance e-government to facilitate the creation of quality jobs.Track C. 4th Industrial Revolution: Workforce

Changes and Jobs in the Upcoming Intelligence and Information Age
Yonghyun Kwon (Ministry of Science, ICT and Future Planning)
Data is the key to the development of artificial intelligence. Algorithms are enhanced autonomously through data. Without data, even the smartest scientist is unable to create good artificial intelligence. The Fourth Industrial Revolution will change the structure and features of businesses. Unlike the past, in the Fourth Industrial Revolution, labor and lowering the unit cost of equipment investments are not sources of competition.
There are optimistic and pessimistic views toward employment in the
Fourth Industrial Revolution. However, the basic repeated demand for jobs will be reduced. Current social policy systems for employment are based on the assumption that all adult men and women will receive secured incomes from their workplace for a lifetime. However, the future industrial structure will be different as companies will provide goods and services according to market data and change the required jobs occasionally based on market demand.
The Future of Advancements in Technology and Jobs
Doowon Cha (KISTEP)
Among the core values for the future is hyper connectivity. Economic
agents, industries, academia, culture, stratums, and existing national
resources will be connected efficiently and produce a society with new values and opportunities for growth, by eliminating the constraint of time and space. In the age of robotics devices, resolving literacy and digital divide will be a major issue, as the middle class will decrease and polarization will be intensified.
The Influence of Artificial Intelligence on Future Job Market
Gayeol Park (Korea Employment Information Service)
As technology develops, societal acceptance of technology becomes
important. Economic efficiency and an acceptance procedure within
society are as important as the technological aspects. In the short term, the strategy for future labor market should conduct a rigorous
analysis for jobs at risk of being replaced, and prepare for job changes. In the long-term, there must be a labor law framed around intelligence information platforms and an education system based on creative collaboration. In addition, results for technological innovations should be shared in society. Cooperation in the areas of policy systems, spread of education, and research development is vital.
Jobs in the Fourth Industrial Revolution
Donghyun Lee (SPRI)
In the Fourth Industrial Revolution, the role of SW in resolving issues
will be magnified through automation, optimization, and flexibilization.
The three elements of the SW Revolution, which is identical to the
Fourth Industrial Revolution, are data integration, artificial intelligence, and user interface. There are differences in past SW technology regarding the range detectable, autonomous judgment, and ability to execute. Nevertheless, there are differences regarding technology between South Korea and advanced countries; South Korea is ranked 25th in the world in terms of the level of preparation in adjusting to the industrial revolution. South Korean companies are unprepared and linger around the level of automation and expansion of communication facilities. In this situation, specialists predict that five million jobs will disappear by 2020 and 63% of South Korean professionals are at risk for the upcoming 10 to 20 years. There are conflicting opinions on the future of jobs among specialists. The fear of job replacement has persisted for over 200 years since the Industrial Revolution. Conversely, the introduction of new technology offers equivalent and supplementary jobs.
New Attempts in Jobs in the Future
Youngseng Kim (KRIVET)
Through structural changes for artificial intelligence and business,
the development of technology is predicted to bring about changes
to types of work conditions and lifestyles over employment types and
automation. If the current pyramid structure continues, ICT will create a closed society. In contrast, by breaking free from the pyramid structure and activating ventures, seeking qualitative growth, and creating a society with more self-directed jobs and self-employment, there will be a shift to a society with many valuable medium-sized businesses. We should work toward this goal. Once value chains and industrial ecosystems have been activated, change becomes difficult to generate. Therefore, in creating policies for the intelligence information industry, the advancement of major corporations, medium-sized businesses, and the national economy in creating jobs should be considered.Track D. 4th Industrial Revolution: Technology

Automobile and Aircraft Human-Machine Interface
Jihyun Yang (Kookmin University)
After airplanes have been developed with an autopilot function, several studies looked into the problems that could occur from automation. Automobiles and aircrafts share many similarities that allow for benchmarking. Their main difference is in their management agent. Although cars can be driven by anybody theoretically, airplanes are controlled by people who have received a high level of training. From the view of HMI, airplanes have a much more contained problem, whereas cars involve complex issues regarding the characteristics of a much broader demographic. AlphaGo calculates successfully during matches; its stones were placed by Professor Aja Huang, an engineer from Google. Although the artificial intelligence itself had an algorithm, it was not connected to the physical entity. The hardware in automobiles is faster than humans. If there were a safer software (e.g., HMI) that could keep up, it will have a great ripple effect in real life and be the self-driving car that one imagines.

The Prospective for the Drone Industry
in the Fourth Industrial Revolution
Bosung Lee (Korea Aerospace Research Institute)
Drones, a combination of IT and aircraft technology, are currently used mainly for filming and have increased value through uniting with the traditional industry. Ventures relevant to drones are possible with only a computer, basic board, and kit. Specialized services can be provided after purchasing drones for everyday use. In the long-term, outsourcing businesses offering commissioned drone services for businesses will be successful. Drones are compatible with the characteristics of South Korean industry where IT programmers and high-tech manufacturing businesses can be united. Moreover, as the South Korean communication network is well developed, the existing communication network for everyday use can be applied. Following the smartphone market, drones may be the next platform to go beyond the niche market.

Intelligent Assistive Technology for Senior Citizens and the Disabled
Sungpil Kim (J.MARPLE)
Recently, rehabilitation robotics has been a controversial issue in
assistive technology. Even wheelchairs, which are considered a symbol of assistive technology, are being modernized through added arms. Assistive technology is also developing through the integration of many skills, such as partial replacements for muscles and an analysis of sentences that have been typed for word prediction through artificial intelligence technology. However, there have also been cases where issues that have existed in assistive technology were solved through unexpected forms of technology. For instance, although taxis were a difficult mode of transport for people with disabling hearing loss to use, the introduction of Kakao Taxi, which merely requires one to type the location and destination into his/her smartphone, has solved the problem. The example of Kakao Taxi shows that the focus is not necessarily to produce technology specifically targeted to people with disabilities but to consider them while creating technology for better efficiency.
VR/AR Technology in the Fourth Industrial Revolution
Junsung Bang (ETRI)
Virtual and artificial realities offer us a new space. As people are interested in forming social networks in virtual space, virtual reality will develop separate personal and shared spaces. Moreover, as headmounted display (HMD) performance is enhanced, various interaction functions and participatory contents will emerge. As HMD functions are advanced, there are currently contents that offer different storytelling based on people’s actions. To create these participatory contents, understanding of how users act and communicate in virtual reality is the most important factor. We should also consider and prepare for copyright concerns for works produced in other space-time, personal information issues arising from customized services, information inequality problems, and the control of unethical actions in advance.

Intelligent Automobiles, the Research Trend for Autonomous Technology
Euntae Kim (Yonsei University)
There is a difference between traditional automobile manufacturing companies and IT businesses in the development of self-driving cars. For car manufacturing companies, such as Mercedes-Benz and BMW, safety is the main concern when the car is operated and the development method has occurred from Level 1 step-by-step. For IT manufacturing companies, bringing the technology to life is the most important issue and research has been conducted from Level 4. Currently, IT businesses, computer companies, and circuitry businesses have merged. Self-driving technology may come to life soon.
Contact Us
Barun ICT Research Center
50 Yonsei-ro, Seodaemun-gu, Seoul 03722, Korea
Tel : +82-2-2123-6694
Email : barunict@barunict.kr